Unsecured IoT – A Dangerous Gambit!
By: Darin Barton CISSP, CISA
In October 2016, one of the world’s largest and most devastating DDoS attacks occurred through IoT (Internet of Things) devices. This was not a complex attack, in fact, it was as simple as it was devastating and affected several major sites including: Amazon, Twitter, Spotify, Netflix and others.
How Did This Attack Happen?
A botnet called “Mirai” scanned the Internet for IoT devices which used default user names and passwords. These devices were then enlisted to engage targets with noise until they could no longer accept legitimate traffic. This attack was designed to focus on DVR camera systems manufactured by a Chinese company called XiongMai Technologies. The “Mirai” creator obviously had knowledge that the firmware’s username and password were hard coded and open to compromise. But XiongMai is not the only company with exploitable vulnerabilities. According to Rapid7, nearly 20 brands of closed-circuit TV (CCTV) security cameras are affected by a vulnerability in the Ray Sharp DVR platform allowing unauthenticated access to device configuration settings.
Through flaws in the DVR web interface, a hacker could gain remote access and full administrative control of the camera system or get access to other networked devices behind a firewall.
Why is this attack so important?
It clearly shows the weaknesses within IoT devices that we so freely bring into our businesses, homes and other trusted venues. This brings IoT to the forefront of cybersecurity. The vulnerabilities are real, the threat is prevalent and we need to take action.
To be honest, I always thought an IoT attack would come from an appliance with software embedded directly during the manufacturing process. This made sense because most IoT devices are not accessible from the Internet. We may provide controlled Internet access from an IoT device to the manufacturer or from the manufacturer to the IoT device through a VPN but those connections are typically well controlled and policy enforced. But does that mean you are safe? Absolutely not.
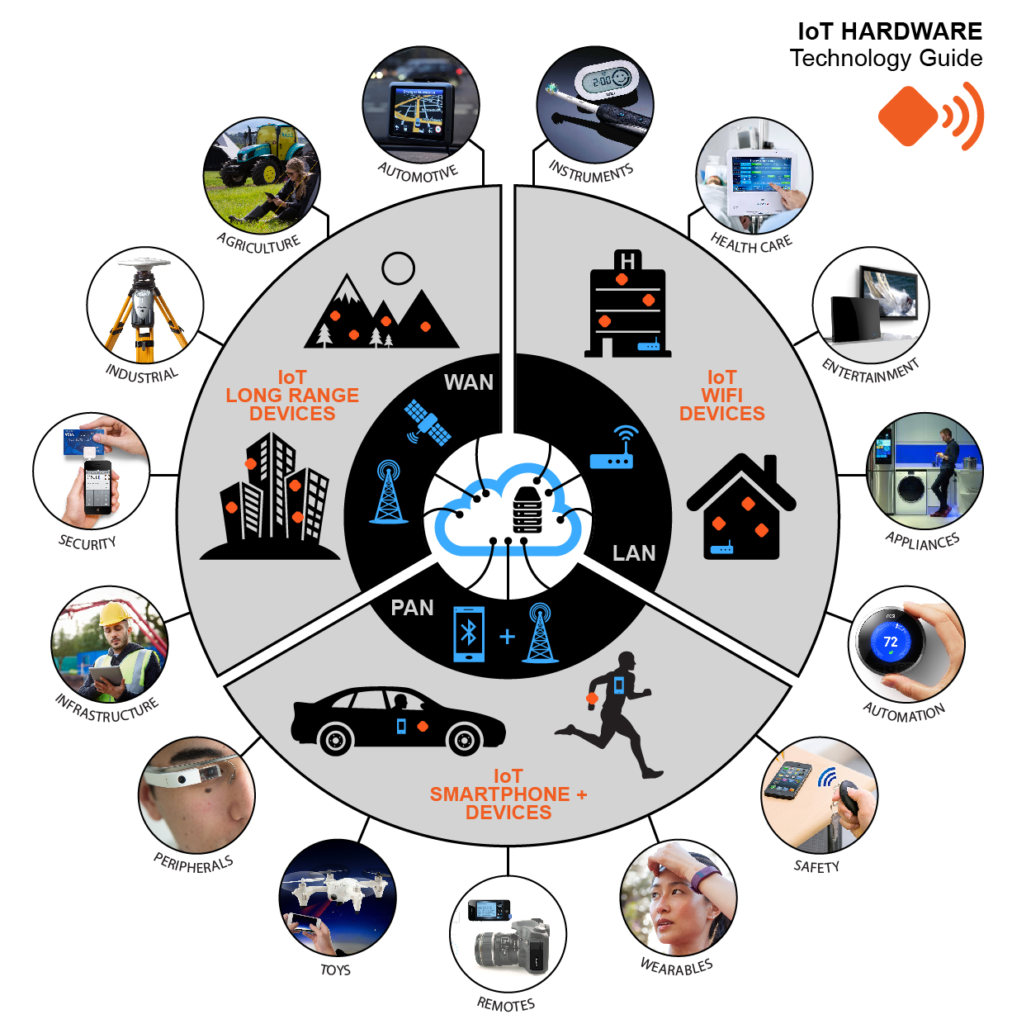
How many IoT devices do you have within your business environment? Let’s make a quick list:
- Smart TVs
- Mobile Devices
- Computers and Laptops
- Wireless Access Points
- Printers, Copiers & Scanners
- Cameras & DVR
- Watches
- GPS Systems
- Vehicles
- Fridges
- Microwaves
- Toasters
- Washing Machines
- Dryers
- Dishwashers
- eReaders
- Alarm systems
- Access Control Systems
- Lights
- Speakers
- Boilers and Chillers
- Furnaces
- Air Conditioner Systems
- Farming Equipment
- Smart Energy Monitoring
- Toys
- Healthcare devices
and much more….
You may scoff at some of these but there are two legitimate truths to recognize:
- By 2020, there will be over 40 billion IoT devices accessible on the Internet.
- Historically, we have put too little effort into securing our internal networks (and our privacy).
WHAT CAN YOU DO?
The first and best course of action is to accept that IoT is here to stay. Begin thinking about the vulnerabilities this technology brings to your environments and plan how you intend to secure it. This doesn’t need to be complex, in fact, most organizations are already segmenting their networks into secure zones so adding an IoT segment just makes sense. But, here is a list of cybersecurity basics you can use to secure your IoT architecture:
- Identify all IoT assets
- Segment those devices into their own VLAN
- Do not NAT directly to your DVR systems (use a VPN client with strong or two-factor authentication to connect to your internal network)
- Route all IoT segments through a firewall, preferably one with UTM functionality.
- Set policy enforcement against IoT VLANS and control how IoT devices communicate with other networks
- Ensure IPS, malware and botnet scanning is applied to all inbound/outbound traffic against those VLANs
- Configure the ability to automatically isolate compromised devices from the network
- Have consistent monitoring and alerting against all IoT devices
In conclusion
Don’t fight IoT – embrace it – but take the time to properly secure your IoT infrastructure.
:Darin Barton CISSP, CISA is a senior security professional in Toronto Canada, with 20+ years experience in cybersecurity and investigations and currently employed with Access 2 Networks Inc. (A2N).